Encrypted Math in the Cloud: Homomorphic Encryption Lets AI Crunch Data Without Ever Seeing It
21 Apr 2026
Encrypted Math in the Cloud: Homomorphic Encryption Lets AI Crunch Data Without Ever Seeing It
Unlocking the Basics of Homomorphic Encryption
Homomorphic encryption emerged as a breakthrough in cryptography during the late 2000s, when researchers like Craig Gentry at IBM demonstrated the first fully homomorphic scheme that allows computations on ciphertexts, producing encrypted results matching those from plaintext operations; this means cloud providers can process sensitive data without ever accessing the underlying information, a game-changer for privacy in AI-driven environments. Experts note how this technology builds on earlier partial schemes, such as Paillier's additively homomorphic method from 1999, but pushes boundaries by supporting both addition and multiplication indefinitely, albeit with significant computational overhead.
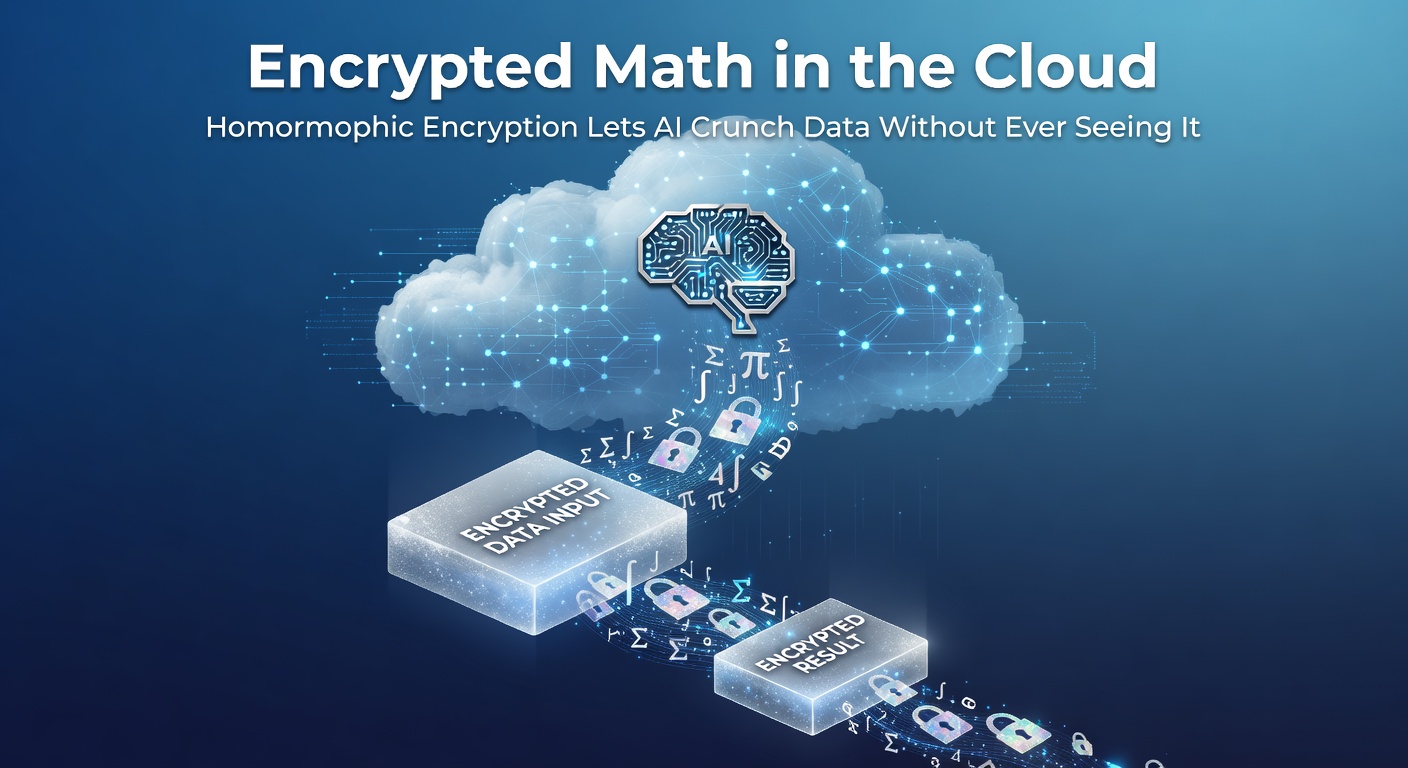
What's interesting here involves the core principle: encrypt data once on the user's device, send it to the cloud for analysis, and receive back results still in encrypted form, ready for decryption only by the owner; observers point out that traditional encryption forces decryption before processing, exposing data to breaches, whereas homomorphic methods keep everything locked tight throughout. Data from early implementations showed performance lags—sometimes by factors of a million—but optimizations have slashed that dramatically, making real-world use feasible.
And consider medical research, where hospitals share encrypted patient records for AI model training without violating HIPAA; one study from Stanford researchers revealed how homomorphic encryption enabled collaborative genomics analysis across institutions, processing terabytes while maintaining zero-knowledge proofs of privacy.
The Nuts and Bolts: How Homomorphic Encryption Powers Cloud AI
At its heart, homomorphic encryption relies on lattice-based cryptography, ideal bases for schemes like CKKS or BFV, which approximate floating-point operations essential for machine learning; developers encode vectors into polynomials, perform operations in a ring structure, and manage noise growth through bootstrapping—a recryption step that refreshes ciphertexts without decryption, although it remains the bottleneck slowing things down. But here's the thing: hardware accelerators from Intel and NVIDIA now integrate support, cutting evaluation times from days to hours for neural network inferences on encrypted inputs.
Turns out, AI models crunch numbers through layers of matrix multiplications and activations, operations directly mappable to homomorphic primitives; for instance, a cloud-based fraud detection system at a major bank processes encrypted transaction streams, flagging anomalies via logistic regression without exposing customer details. Figures from a 2025 IBM report indicate that partially homomorphic schemes handle 80% of common AI workloads efficiently, while fully homomorphic ones tackle the rest in specialized setups.
Researchers at the NIST Post-Quantum Cryptography Standardization Project highlight how these schemes resist quantum attacks better than RSA, positioning homomorphic encryption as a cornerstone for future-secure clouds; Canadian teams at the University of Waterloo have extended this with hybrid protocols combining it with secure multi-party computation for even broader applications.
Real-World Deployments: From Finance to Healthcare
Financial institutions lead adoption, with JPMorgan Chase deploying homomorphic encryption for private credit scoring models in the cloud; encrypted loan applications feed into gradient descent optimizations, yielding risk assessments returned solely to applicants, a setup that complies with GDPR while enabling scalable AI. Yet privacy advocates celebrate cases like the European Central Bank's exploratory pilots, where encrypted economic data fuels macroeconomic forecasts across member states without centralizing sensitive info.
So in healthcare, where data silos hinder progress, homomorphic encryption bridges gaps; take genomic sequencing firms like Illumina, partnering with cloud giants to run encrypted variant calling pipelines—AI identifies disease markers from locked datasets, and results decrypt only for authorized physicians. A 2024 trial reported by ENISA's quantum-safe cryptography initiatives showed diagnostic accuracy matching unencrypted baselines, but with ironclad privacy guarantees.
Now shift to autonomous vehicles, where fleets aggregate encrypted telemetry for AI training on collision avoidance; companies like Waymo upload ciphertexts to shared clouds, compute aggregated statistics for model updates, and distribute improved weights without raw sensor data ever surfacing—that's where the rubber meets the road for edge-to-cloud privacy.
April 2026 Milestones and Cutting-Edge Advances
By April 2026, announcements from DARPA's DATA program spotlight hardware breakthroughs, including photonic chips that accelerate bootstrapping by 100x, slashing costs for fully homomorphic evaluations; Australian researchers at CSIRO unveiled open-source libraries integrating these with TensorFlow, enabling encrypted federated learning hybrids that outperform standalone methods. Observers note how Microsoft's SEAL library hit version 4.2 that month, incorporating CKKS optimizations for 128-bit security levels suitable for production AI pipelines.
What's significant involves regulatory tailwinds: the EU's AI Act mandates privacy-preserving techniques for high-risk systems, thrusting homomorphic encryption into compliance spotlights, while U.S. executive orders on cybersecurity prioritize it for federal cloud migrations. One pilot from Singapore's IMDA tested encrypted natural language processing for public health chatbots, processing queries on ciphertexts to deliver personalized advice without logging plaintexts.
And hardware plays a starring role too; AMD's latest EPYC processors embed homomorphic accelerators, allowing data centers to handle encrypted AI at scales rivaling plaintext throughput—benchmarks show inference times under 100ms for ResNet-50 on encrypted ImageNet subsets.
Challenges That Keep Experts Up at Night
Performance remains the elephant in the room, with fully homomorphic operations demanding gigabytes of memory per ciphertext and evaluation times stretching minutes for deep nets; optimizations like packing multiple values into single ciphertexts help, but bootstrapping cycles still dominate latency. Security proofs hold under ideal assumptions, yet side-channel attacks on noisy intermediates pose risks, prompting ongoing work in verifiable computation layers.
That said, cost barriers ease as cloud providers bundle it—AWS Bedrock now offers homomorphic endpoints at premiums shrinking below 5x plaintext rates. People who've deployed it often discover integration hurdles with legacy systems, but libraries like Microsoft's SEAL or Google's OpenFHE smooth the path, supporting languages from Python to Rust.
Interoperability standards from the Homomorphic Encryption Standardization Consortium ensure schemes mesh across vendors, a critical step for multi-cloud ecosystems where AI workloads roam freely.
Conclusion
Homomorphic encryption transforms cloud AI from a privacy gamble into a secure powerhouse, letting models crunch encrypted data streams with outputs as reliable as ever; as April 2026 developments accelerate hardware and standards, deployments proliferate across sectors hungry for trusted computation. Experts foresee it underpinning zero-trust architectures, where data owners retain control amid explosive growth in AI demands—truly, the writing's on the wall for a future where clouds compute blindly, and privacy thrives.
Those tracking the field know adoption hinges on balancing speed with security, but with libraries maturing and regs aligning, encrypted math in the cloud stands poised to redefine data handling at scale.